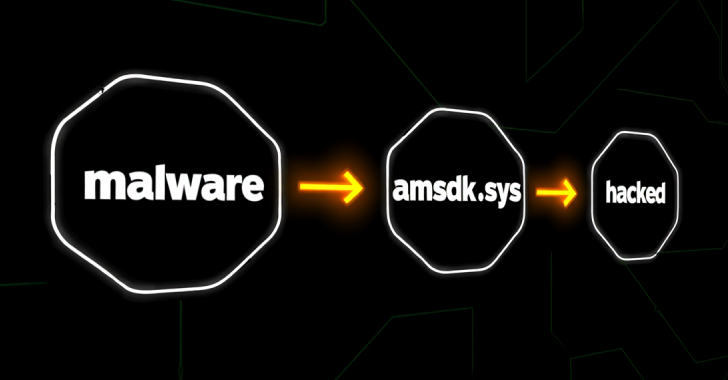
The threat actor known as Silver Fox has been attributed to abuse of a previously unknown vulnerable driver associated with WatchDog Anti-malware as part of a Bring Your Own Vulnerable Driver (BYOVD) attack aimed at disarming security solutions installed on compromised hosts.
The vulnerable driver in question is “amsdk.sys” (version 1.0.600), a 64-bit, validly signed Windows kernel device driver